Securely Working with phpinfo
Important security considerations when working with phpinfo on your Pantheon Drupal site.
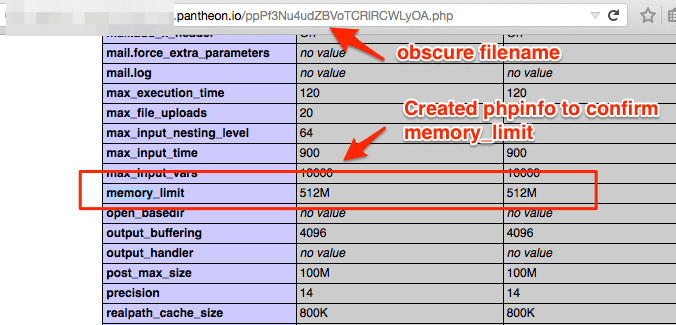
This section provides information on steps you can take to obscure your phpinfo online.
Pantheon provisions isolated Linux containers with an optimized PHP stack. The php.ini is part of a highly tuned configuration and is not user-configurable. We continually deploy new builds of PHP and you also have the ability to upgrade PHP versions.
You can use phpinfo to see a comprehensive list of what's installed with the version of PHP in use by a particular environment. We also have example PHP info for each version of PHP on the platform.
Important Security Notes
-
phpinfoexposes sensitive information, including the password to connect to the DB -
Delete any
phpinfofile you create immediately after review
Drupal Note
Drupal makes the phpinfo available to privileged users at https://example.com/admin/reports/status/php
Review phpinfo
Follow the steps below to keep your phpinfo file secure.
-
Lock environment (if the environment does not currently need to be publicly accessible).
-
Create a php file with an obscure filename that uses
phpinfo. -
Omit sensitive sections from the
phpinfooutput to minimize the information exposed over the web. The recommended way to callphpinfois: -
Visit the file in a web browser to view
phpinfo.
- Delete the file immediately so you do not expose sensitive information, such as the password used to connect to the DB.
Terminus
You can use Terminus to check your phpinfo values as an alternative to exposing information on a web-accessible URL: